Bitwarden CLI Supply Chain Attack: What Developers Need To Know
The Bitwarden CLI npm package was briefly compromised in a supply chain attack, exposing developers to credential theft risks. Learn what happened, what was affected, and how teams can secure their CI/CD pipelines, npm packages, and developer environments.
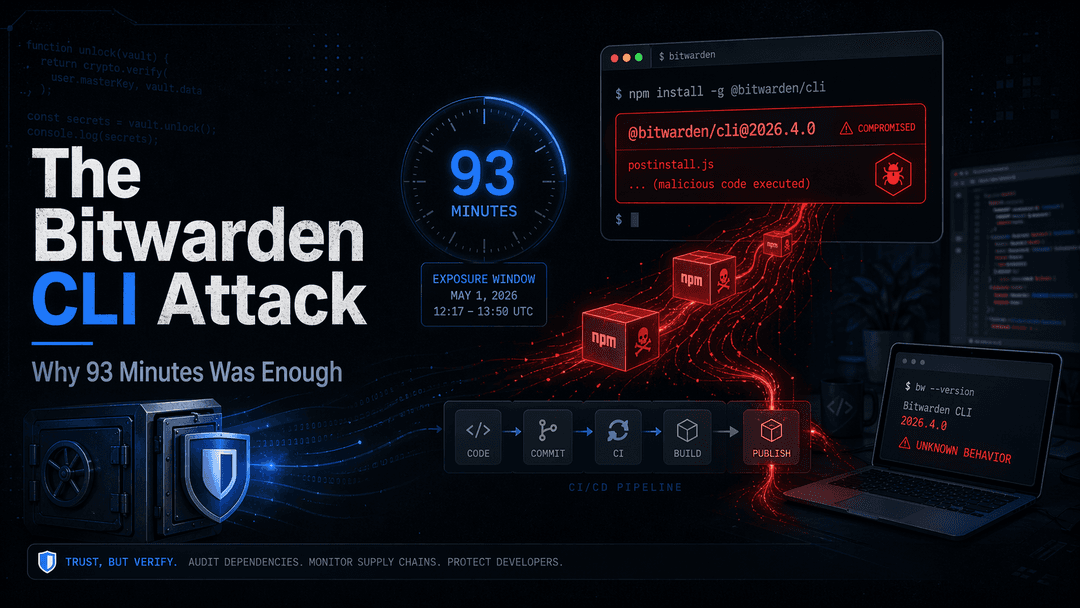
On April 22, 2026, a malicious version of the Bitwarden CLI package was published to npm.
The affected version was:
@bitwarden/cli@2026.4.0
It was live for only around 93 minutes, but that was enough to create serious risk for developers who installed it.
This was not a Bitwarden vault breach. Bitwarden stated that vault data, production systems, browser extensions, desktop apps, and mobile apps were not affected.
The issue was limited to the npm CLI package during a short window.
What Happened
Attackers published a malicious npm version of Bitwarden CLI.
The package used a preinstall hook, which means the malicious code could run automatically during installation.
That is what makes this type of attack dangerous.
A developer does not need to click a suspicious link.
They do not need to run an unknown file.
They just install a package they already trust.
What The Malware Targeted
The malware reportedly looked for developer secrets such as:
- GitHub tokens
- npm tokens
- SSH keys
.envfiles- Cloud credentials
- Shell history
- GitHub Actions secrets
- AI and MCP tool configs
This matters because developer machines often have access to source code, deployments, cloud accounts, and production systems.
One infected machine can expose much more than one local environment.
Why This Matters
The malware could also spread.
If it found npm tokens with publishing rights, it could inject malicious code into other packages owned by the victim.
That turns one compromised install into a possible supply chain chain reaction.
This is the real lesson.
Modern attacks do not always start in production.
They can start from a package install, a CI workflow, or a developer laptop.
What Teams Should Learn
Teams should review how they manage:
- npm install scripts
- package publishing rights
- GitHub Actions permissions
- local developer secrets
- cloud credentials
- AI coding tool configs
- token rotation processes
The Bitwarden CLI attack was short.
But short does not mean harmless.
In software supply chain security, even 93 minutes can be enough.
Modern security is not just about protecting the app.
It is about protecting everything that builds, ships, and maintains the app.