OpenAI's Daybreak: The Security Gap in Vibe-Coded Apps
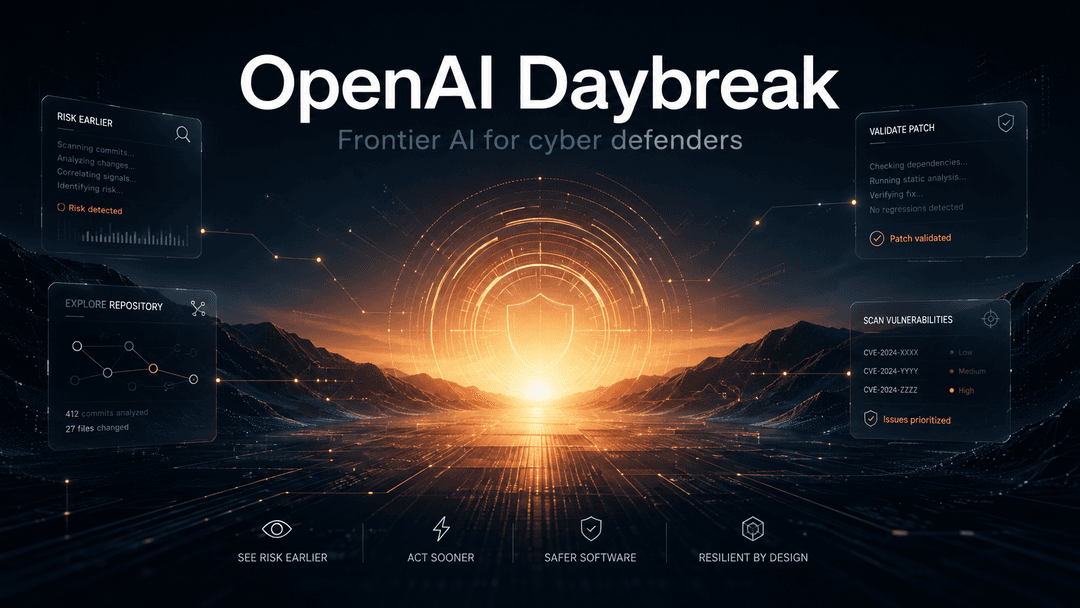
OpenAI just launched Daybreak, an AI cyber defense platform powered by GPT-5.5.
OpenAI just launched Daybreak. If you're running an app, especially one your team built with AI, you should pay attention. Mostly because the headline news is good. Partly because the part nobody is saying out loud matters more.
What Daybreak actually is
Daybreak is OpenAI's new push to use AI for cybersecurity defense. Think of it as a very smart assistant that can read your entire codebase, spot security holes, write fixes, and check that the fixes work. It runs on GPT-5.5 plus a specialized variant called GPT-5.5-Cyber, with OpenAI's coding agent Codex doing the heavy lifting.
The numbers are real. OpenAI says an earlier version (GPT-5.4-Cyber) already helped fix over 3,000 vulnerabilities. The partner list is the who's who of enterprise security: Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Akamai, Snyk, Semgrep, Trail of Bits.
This isn't a demo. It's a product.
The defender's math just changed
For decades, attackers had an unfair math problem on their side. They only needed to find one hole. Defenders had to find them all.
AI starts to flip that math. A model that reads your full codebase in minutes and flags risk continuously is exactly what defenders have been missing. Daybreak (and Anthropic's Project Glasswing before it) is the start of defenders finally catching up.
If you run a startup, this trend reaches you eventually. Cheaper, faster, better automated security checks are coming. That's good.
The part nobody is saying out loud
Daybreak is brilliant at finding bugs that look like other bugs. SQL injection patterns. Known dependency vulnerabilities. Missing input validation. The catalog of mistakes the internet has documented a million times.
It is much weaker at the things that actually break apps built with AI assistance.
The login flow that looks fine but lets a signed-in user pull another user's data, because the AI forgot to add a permission check. The Stripe webhook handler that processes a refund without verifying the signature. The AI agent with database access that will happily run whatever a customer types into it. The admin endpoint that's "protected" because the AI assumed everyone hitting it was supposed to be there.
These aren't pattern-matching bugs. They're business logic mistakes. A model trained on past vulnerabilities will often miss them, because they look correct in isolation. They only break when you actually understand what your app is supposed to do, and who is supposed to do what.
That gap is wider in vibe-coded apps and AI agent deployments. Not because the code is worse, but because the team often didn't write it line by line. The mental model of "what should never happen here" was never fully built. AI defenders can't reconstruct it for you.
What this means for you
If you're shipping AI-built software, don't read Daybreak as "now I don't need to think about security." Read it as confirmation that security is a moving target everyone is racing toward.
The teams that win are going to do two things in parallel.
One, use AI defenders for what they're good at. Continuous code scanning, dependency tracking, the boring repeat work that should never have been manual.
Two, get human eyes on the stuff AI can't see. Your business logic. Your agent permissions. Your trust boundaries. The places where "it runs" and "it's safe" are not the same sentence.
Daybreak is sunrise. It's not the sun.